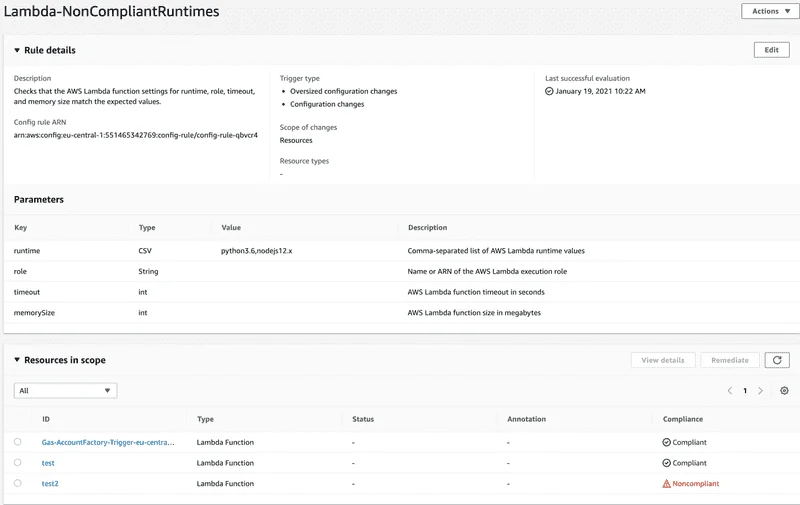
.Detect noncompliant Lambda runtimes in your environment
A few days ago the Python Software Foundation (PSF) annouced that Python 2.7.18 was the final release of Python 2. With it's release, the PSF states that “As of January 1st, 2020 no new bug reports, fixes, or changes will be made to Python 2, and Python 2 is no longer supported.” In addition, AWS announced that Lambda will only support Python 2.7 until June 1, 2021. This phenomenon will overtake us again and again with other programming languages. Furthermore, it is advisable to always keep your Lambdas up to date with the latest programming languages versions in order to prevent security gaps and to gain the latest features. Here is a simple way to find out which lambdas in your environment are not compliant with the latest programming languages.
Since we want to use an AWS Config Rule to detect not compliant Lambda runtimes - we need to ensure that AWS Config is activated in your AWS Region. There are multiple ways to enable Config - you can use Infrastructure as Code (Terraform - CloudFormation - CDK) or just do it using the Console ⛔️ Not a best practice ⛔️.
After we have enabled Config - we are able to deploy the AWS managed Config rule that checks for Lambda function settings eg. runtime. Here is a CloudFormation template to deploy the managed rule. If you want to adjust the compliant Lambda runtimes you just need to update the parameter CompliantLambdaRuntimes.
# Author: David Krohn
AWSTemplateFormatVersion: 2010-09-09
#-----------------------------------------------------------------------------
#Parameters
#-----------------------------------------------------------------------------
Parameters:
CompliantLambdaRuntimes:
Type: String
Default: python3.6,nodejs12.x
Description: CompliantLambdaRuntimes (Commaseperated)
#-----------------------------------------------------------------------------
#Resources
#-----------------------------------------------------------------------------
Resources:
CheckForNonCompliantLambdaRuntimes:
Type: AWS::Config::ConfigRule
Properties:
ConfigRuleName: Lambda-NonCompliantRuntimes
Description: Checks that the AWS Lambda function settings for runtime, role, timeout, and memory size match the expected values.
InputParameters:
runtime: !Ref CompliantLambdaRuntimes
Source:
Owner: AWS
SourceIdentifier: LAMBDA_FUNCTION_SETTINGS_CHECKIf you want to deploy the managed rule using the Console you just need to go to AWS Config > Rules > Add rule and select the rule lambda-function-settings-check. This rule will help us to identify noncompliant Lambda runtimes. We just need to pass compliant runtimes comma-seperated to the runtime parameter eg.: python3.6,nodejs12.x. At the end the result in the AWS Console would look like this:
We use cookies on our website. Some of them are essential,while others help us to improve our online offer.
You can find more information in our Privacy policy
